On March 2nd, 2026, we received a submission through our Bug Bounty Program for a Remote Code Execution vulnerability in Kali Forms, a WordPress plugin with more than 10,000 active installations. This vulnerability makes it possible for an unauthenticated attacker to execute code on the server. The vendor released the patched version on March 20th, 2026, and we originally disclosed this vulnerability in the Wordfence Intelligence vulnerability database on the same day. Our records indicate that attackers started exploiting the issue the same day, on March 20th, 2026. The Wordfence Firewall has already blocked over 312,200 exploit attempts targeting this vulnerability.
Wordfence Premium, Wordfence Care, and Wordfence Response users received a firewall rule to protect against any exploits targeting this vulnerability on March 5, 2026. Sites using the free version of Wordfence received the same protection after the standard 30-day delay on April 4, 2026.
Considering this vulnerability is under active attack, we urge users to ensure their sites are updated with the latest patched version of Kali Forms, version 2.4.10 at the time of this writing, as soon as possible.
Vulnerability Summary from Wordfence Intelligence
Vulnerability Details
Examining the code reveals that the plugin uses the _save_data() function in the Form_Processor class to save the form submission in the database.
protected function _save_data()
{
$save = $this->get('save_form_submissions', '0');
if ($save !== '0') {
$arr = [
'post' => $this->post,
'data' => $this->data,
'submission_id' => false,
'extra' => [
'separator' => $this->get('multiple_selections_separator', ','),
],
];
$arr = apply_filters($this->slug . '_save_data', $arr);
$post = wp_insert_post([
'post_type' => 'kaliforms_submitted',
'post_title' => $arr['post']->post_title,
'post_status' => 'publish',
]);
if (is_wp_error($post)) {
return false;
}
foreach ($arr['data'] as $k => $v) {
if ($k === 'kf_hooks' && is_array($v)) {
continue;
}
if (isset($v['image']) && isset($v['label']) && isset($v['price'])) {
$v = $v['label'];
}
$value = is_array($v) ? sanitize_text_field(implode($arr['extra']['separator'], $v)) : sanitize_text_field($v);
update_post_meta($post, $k, $value);
}
$arr['submission_id'] = $post;
$arr = apply_filters($this->slug . '_after_save_data', $arr);
$this->saved = $arr['submission_id'];
}
if (isset($this->placeholdered_data['{entryCounter}'])) {
$this->placeholdered_data['{entryCounter}'] = call_user_func($this->placeholdered_data['{entryCounter}'], $this->post->ID);
}
if (isset($this->placeholdered_data['{thisPermalink}'])) {
$this->placeholdered_data['{thisPermalink}'] = call_user_func($this->placeholdered_data['{thisPermalink}']);
}
When a form is submitted, the prepare_post_data() function loops through the user-supplied data and writes it into an internal array called placeholdered_data, which normally holds placeholder values the plugin uses later (like {entryCounter} or {thisPermalink}). The problem is that there is no allow-list or filtering on which keys the user is allowed to set, so an attacker can freely overwrite these internal placeholders with any value they want. Later on, the _save_data() method takes those same placeholder values and passes them straight into call_user_func(), meaning whatever string the attacker placed into {entryCounter} or {thisPermalink} gets executed as a PHP function. The {entryCounter} placeholder is called with a single argument, which is the post ID loaded from the user-controlled formId parameter. Because WordPress post IDs are always integers, the attacker can call any PHP function, but only with one integer argument.
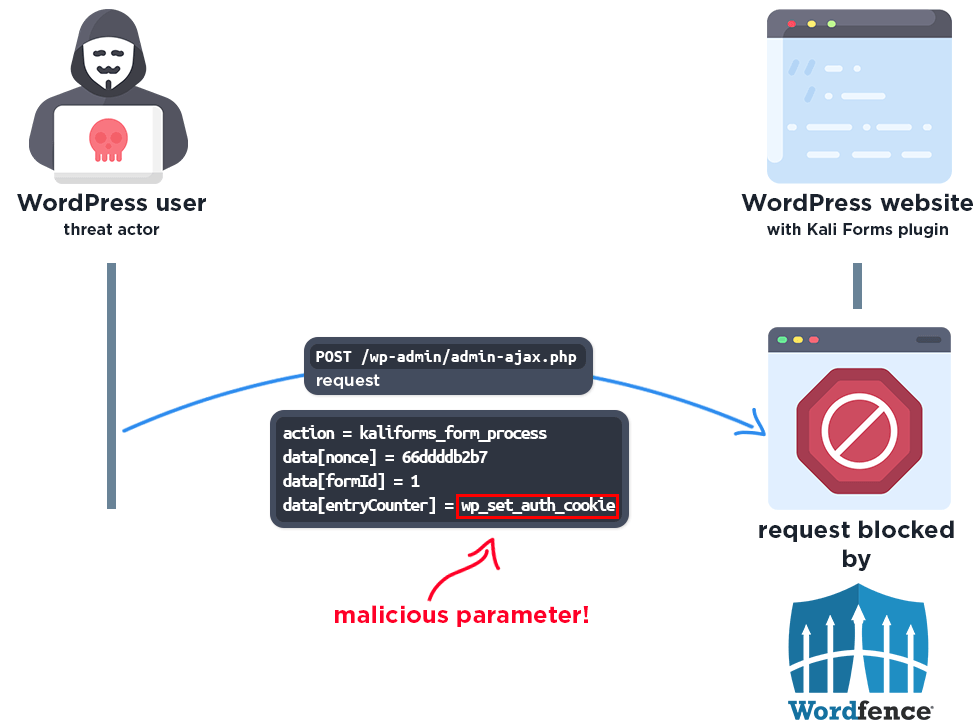
One example of leveraging this vulnerable function call is to achieve authentication bypass: an attacker can set {entryCounter} to wp_set_auth_cookie and submit a formId of 1. The plugin then executes wp_set_auth_cookie(1), and since User ID 1 is normally the default administrator account, WordPress responds with valid admin auth cookies, letting the attacker log in as the administrator without any credentials.
In this case, attackers obtain the admin’s auth cookie with the authentication bypass exploit, and use it to authenticate themselves, allowing them to edit the theme’s functions.php file and add malware code.
A Closer Look at the Attack Data
The following data highlights actual exploit attempts from threat actors targeting this vulnerability.
Example attack request
POST /wp-admin/admin-ajax.php HTTP/1.1 Host: [redacted] Content-Type: application/x-www-form-urlencoded action=kaliforms_form_process&data[formId]=1&data[nonce]=66ddddb2b7&data[entryCounter]=wp_set_auth_cookie
Wordfence Firewall
The following graphic demonstrates the steps to exploitation an attacker might take and at which point the Wordfence firewall would block an attacker from successfully exploiting the vulnerability.
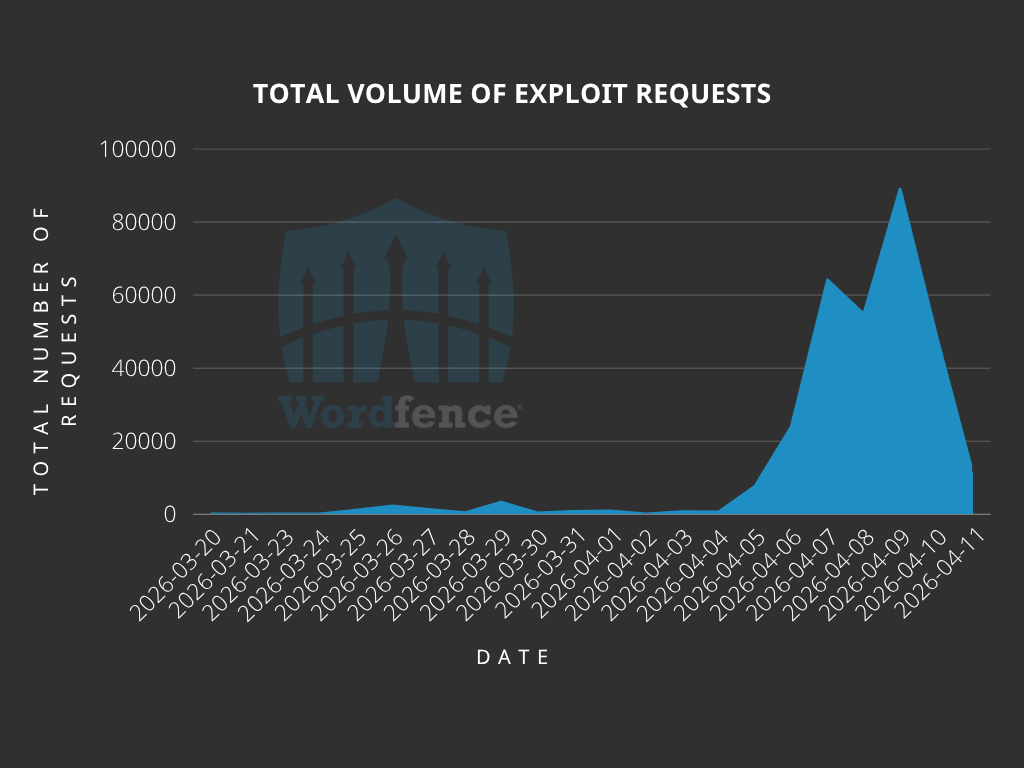
Total Number of Exploits Blocked
The Wordfence Firewall has blocked over 312,200 exploit attempts since the vulnerability was publicly disclosed.
According to our data, attackers started targeting websites the same day the vulnerability was disclosed, on March 20th. We also detected and blocked a large number of exploit attempts from April 4th to 10th.
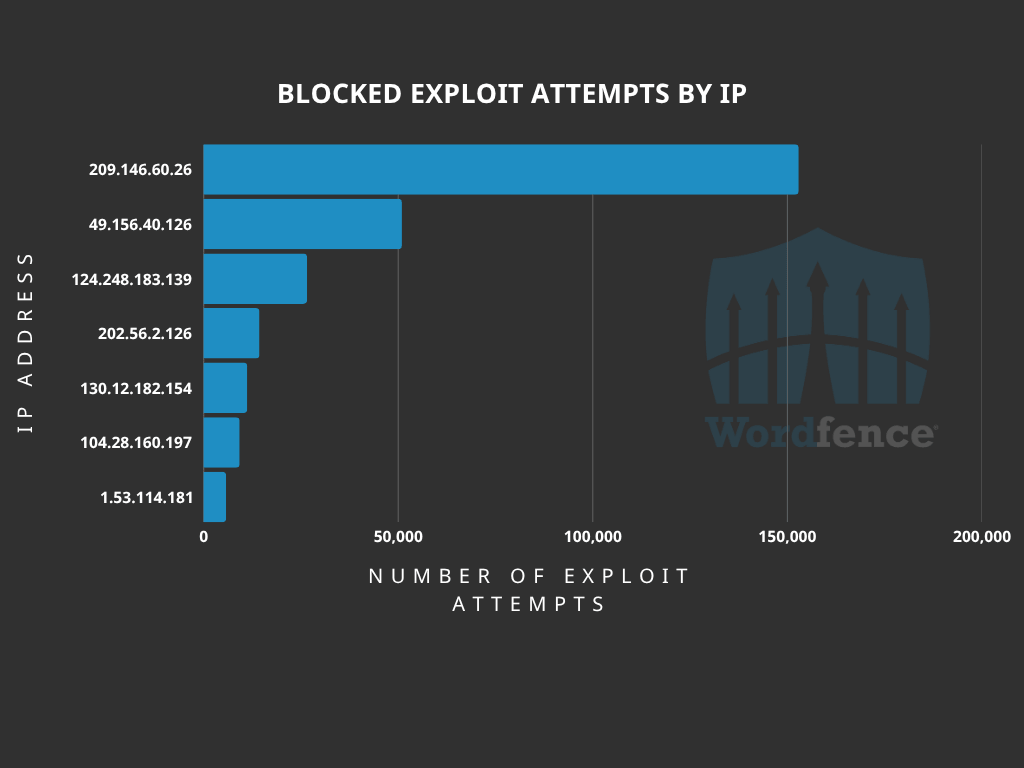
Top Offending IP Addresses
The following IP Addresses are currently the most actively engaged IP addresses targeting the Kali Forms plugin form submission save function:
- 209.146.60.26
- Over 152,000 blocked requests.
- 49.156.40.126
- Over 50,000 blocked requests.
- 124.248.183.139
- Over 26,000 blocked requests.
- 202.56.2.126
- Over 14,000 blocked requests.
- 130.12.182.154
- Over 11,000 blocked requests.
- 104.28.160.197
- Over 9,000 blocked requests.
- 1.53.114.181
- Over 5,700 blocked requests.
- 157.15.40.74
- Over 3,000 blocked requests.
- 114.10.99.126
- Over 2,500 blocked requests.
- 83.147.12.83
- Over 1,300 blocked requests.
Indicators of Compromise
Unfortunately, there are currently no clear or easily identifiable indicators of compromise. If the attackers manage to log in as an administrator, they can easily clear their tracks.
We recommend reviewing log files for any requests originating from the following IP addresses:
- 209.146.60.26
- 49.156.40.126
- 124.248.183.139
- 202.56.2.126
- 130.12.182.154
- 104.28.160.197
- 1.53.114.181
- 157.15.40.74
- 114.10.99.126
- 83.147.12.83
The absence of any such log entries does not guarantee that your website has not been compromised. We recommend doing a thorough review if you see any abnormal activity or accounts on your site, and you are running a vulnerable version of the software.
Conclusion
In today’s article, we covered the attack data for a critical-severity Remote Code Execution vulnerability in the Kali Forms plugin, which could be leveraged to achieve authentication bypass and gain access to administrator accounts. Our threat intelligence indicates that attackers started actively targeting this vulnerability the same day it was disclosed, on March 20th, 2026, with mass exploitation occurring between April 4th and 10th, 2026. The Wordfence firewall has already blocked over 312,200 exploit attempts targeting this vulnerability.
Wordfence Premium, Wordfence Care, and Wordfence Response users received a firewall rule to protect against any exploits targeting this vulnerability on March 5, 2026. Sites using the free version of Wordfence received the same protection after the standard 30-day delay on April 4, 2026.
Even if you have already received a firewall rule for this issue we urge you to ensure that your site is updated to at least version 2.4.10 in order to maintain normal functionality. If you have friends or colleagues using Kali Forms, be sure to forward this advisory to them, as thousands of sites could still be unprotected and unpatched.
If you believe your site has been compromised as a result of this vulnerability or any other vulnerability, we offer Incident Response services via Wordfence Care. If you need your site cleaned immediately, Wordfence Response offers the same service with 24/7/365 availability and a 1-hour response time. Both these products include hands-on support in case you need further assistance.
The post Attackers Actively Exploiting Critical Vulnerability in Kali Forms Plugin appeared first on Wordfence.